By 2026, the smart grid in the GCC has evolved from a pilot concept to the operational backbone of the region’s energy transition. However, this digitalization has introduced a high-stakes reality: the convergence of Information Technology (IT) and Operational Technology (OT) has expanded the attack surface exponentially. The threat is no longer just data theft; it is the potential for physical disruption of critical infrastructure, equipment damage, and widespread blackouts.
Securing these grids requires a fundamental shift in strategy. Generic IT security measures—standard firewalls and antivirus software—are not just insufficient in an OT environment; they can be dangerous. This guide focuses on the specific protocols, standards, and OT security power utilities mindset needed to secure the grid’s core operational functions without compromising the availability that the region relies on.
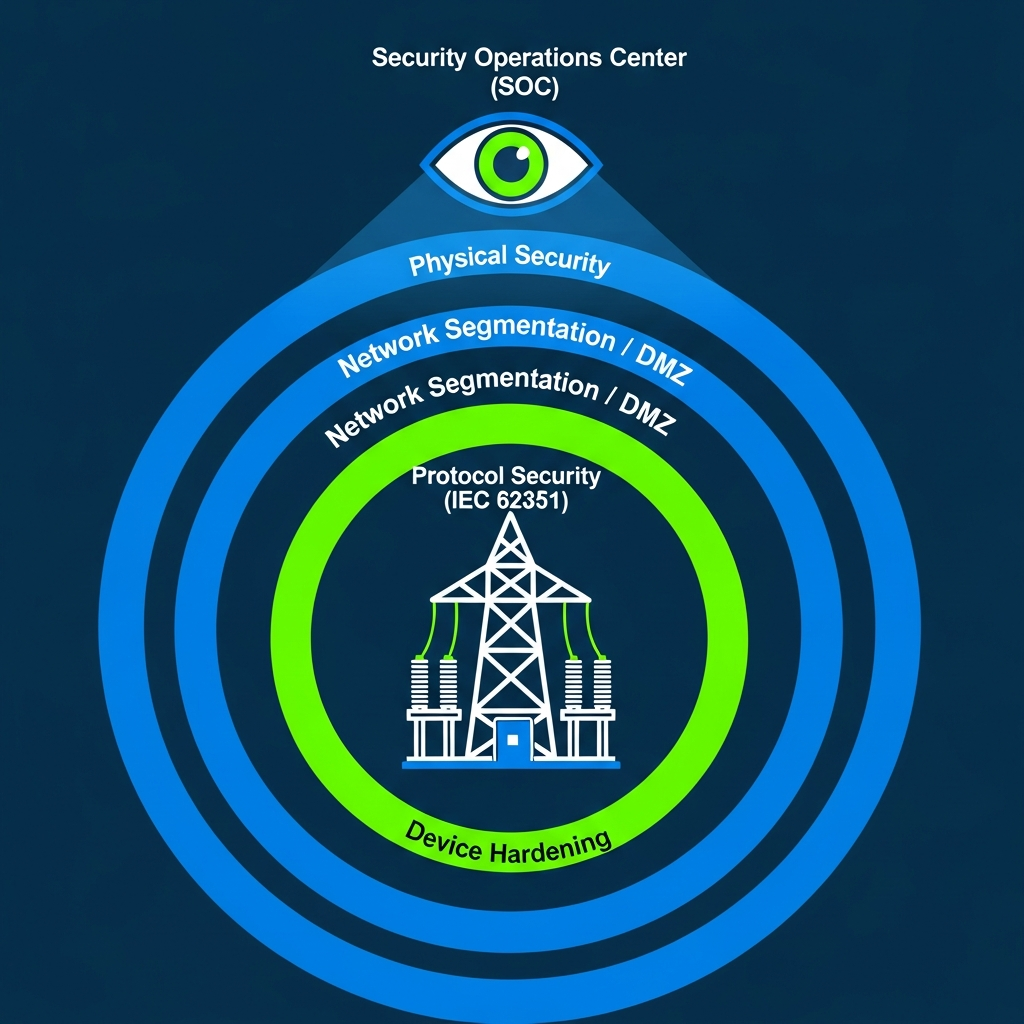
Alt Text for SEO: “Defense-in-depth security model for smart grid OT environments.”
Why Smart Grid Cybersecurity is Different: The OT Security Mindset
In the corporate IT world, security revolves around the CIA triad: Confidentiality, Integrity, and Availability. In the world of smart grid cybersecurity GCC, this triad is inverted.
In OT, Availability and Safety are paramount. A security patch that requires a reboot is acceptable for an email server; it is unacceptable for a turbine controller or a substation relay that must clear a fault in milliseconds. Understanding this distinction is critical. We must implement security controls that “fail open” or degrade gracefully, ensuring that cyber defense never inadvertently causes the very outage it was designed to prevent.
Building a resilient grid? Explore our Smart Grid Technical Advisory and Risk Management services.
Foundational Protocol #1: IEC 62351 – Securing Grid Communication Standards
The global standard IEC 62351 has become the cornerstone for securing the specific protocols that run the grid, such as IEC 61850 (substation automation) and IEC 60870-5-104 (telecontrol).
Key Implementation Aspects:
- Authentication & Encryption: It mandates the use of TLS (Transport Layer Security) encryption for telecontrol messages, ensuring that a “man-in-the-middle” cannot inject false commands to open breakers. For time-critical GOOSE/SV messages within substations, it adds authentication tags to verify the sender’s identity without adding latency.
- Role-Based Access Control (RBAC): It enforces strict user privileges, ensuring that a maintenance engineer cannot accidentally (or maliciously) trip a feeder from a remote HMI.
- The Implementation Gap: A major challenge in 2026 is legacy devices that lack native IEC 62351 support. This requires the deployment of secure protocol gateways or “bump-in-the-wire” encryption devices to protect aging assets.
Foundational Protocol #2: Network Segmentation & the IT/OT DMZ
Network architecture is your first and most critical line of defense. You cannot secure what you cannot segment.
Key Design Principles:
- Unidirectional Gateways: We strongly advocate for data diodes—hardware that physically allows data to flow only one way (from OT to IT). This allows business systems to read grid data for analytics without any physical possibility of sending commands back down to the control network.
- Zone & Conduit Model (IEC 62443): This involves defining strict security zones (e.g., Protection Zone, SCADA Zone, Corporate Zone) and controlling all communication between them through secured conduits (firewalls).
- Deep Packet Inspection (DPI) for OT: Standard firewalls only look at ports. OT-aware firewalls use DPI to inspect the content of the industrial protocols, allowing them to block specific illegitimate commands (e.g., “Write Coil”) while allowing legitimate “Read” commands.
Foundational Protocol #3: Continuous Monitoring & Anomaly Detection
You cannot protect what you cannot see. However, active scanning (pinging devices) is non-negotiable in OT environments as it can crash sensitive PLCs.
Key Actions:
- Passive Network Traffic Analysis (NTA): Deploy tools that sit on the network switch (mirror port) and silently listen to traffic. They build a baseline of “normal” behavior (e.g., RTU A talks to Server B every 5 seconds).
- Alerting on Violations: Set alerts for protocol violations, such as a DNP3 “cold restart” command coming from an unauthorized IP address, or a breaker operation command issued outside of a scheduled maintenance window. This provides early warning of critical infrastructure protection GCC breaches.

Alt Text for SEO: “Timeline of a cyber-physical attack on a utility showing mitigation points.”
The GCC Regulatory Landscape in 2026: Beyond Compliance
Across the GCC, cybersecurity has moved from a recommendation to a license-to-operate issue.
- National Cybersecurity Authorities: Entities like Saudi Arabia’s NCA and the UAE’s Cybersecurity Council have established rigorous Essential Cybersecurity Controls (ECC) and OT-specific frameworks that mandate IEC 62351 compliance.
- Grid Connection Codes: Utilities like DEWA, SEC, and Transco increasingly require evidence of “secure by design” architecture for any new generator or large industrial consumer connecting to the grid.
- Insurance & Liability: Demonstrable cybersecurity maturity is now a primary factor in obtaining cyber insurance coverage and determining liability in the event of a cross-border grid incident.
Building a Mature Security Program: From Protocols to People
Technology is only one pillar of a utility cybersecurity framework 2026. A holistic program requires:
1. Asset & Vulnerability Management for OT
You must maintain a live, automated inventory of all OT assets, including make, model, and firmware versions. This allows for rapid risk assessment when a new vulnerability is disclosed, without needing to walk down every substation.
2. Incident Response Tailored for OT
You need a specific OT incident response playbook. In a cyber event, the priority is keeping the grid stable. This might mean physically isolating a compromised substation and operating it manually rather than simply shutting down servers as you would in IT.
3. Training for Engineers & Operators
Security training must move beyond “don’t click the link.” It must cover social engineering targeting field crews, physical security awareness, and the risks of using personal USB drives on industrial engineering laptops.
Frequently Asked Questions (FAQs)
Q1: What is the biggest cybersecurity weakness in today’s GCC utilities?
Often, it is the converged IT/OT network with weak segmentation and uncontrolled third-party vendor access. Remote maintenance connections used by equipment suppliers, if not meticulously controlled and monitored, are a primary vector for attackers to bypass the perimeter.
Q2: Can we just air-gap our OT network to make it safe?
True air-gaps are largely a myth in modern smart grids. Data must flow for monitoring, billing, and efficiency. The goal is logical segmentation with strictly controlled, monitored, and authenticated data flows. Relying on a presumed air-gap often creates a false sense of security and leads to unmonitored “shadow IT” connections.
Q3: How do we secure legacy equipment that can’t support modern encryption?
This is a major challenge. Solutions include deploying “bump-in-the-wire” encryptors that secure legacy serial links, placing secure protocol gateways at the edge of legacy zones to act as a shield, and implementing compensating controls like stricter physical access and intensified network monitoring around these assets.
Q4: Is cloud adoption compatible with OT cybersecurity for utilities?
It can be, with a hybrid architecture. Highly critical, real-time control (substation protection) remains on-premises. For SCADA historian data, grid analytics, and EMS functions, a private or sovereign cloud with robust encryption and identity management can be secure, but it requires careful design from the ground up.
Conclusion
Smart grid cybersecurity is not a one-time project; it is a continuous journey of risk management. It requires fusing deep power systems engineering knowledge with modern security practices to protect the heartbeat of our economy.
Secure the foundation of your nation’s energy transition. Our smart grid advisory team combines power systems engineering with specialized OT cybersecurity expertise to help GCC utilities design, assess, and harden their critical infrastructure against evolving threats.
Contact us for a confidential discussion on your security readiness or project requirements.
